
Spraying the Microsoft Cloud
Adversaries continue to probe and make entry via the cloud perimeter of organisations. Multi-Factor Authentication (MFA) and additional security controls such as Conditional Access Control makes this a bit more challenging. In December 2021 Mandiant covered an incident where MFA push notification feature was abused to gain access to user accounts. In this write-up we will be going through various ways of detecting pre-cursors of MFA configuration probing and password spraying attacks in Microsoft 365 (M365). This write-up is based on four well documented Open Source Offensive Security Testing tools.
Tools that were executed as part of this research:
- MFASweep ( https://github.com/dafthack/MFASweep)
- o365spray (https://github.com/0xZDH/o365spray)
- MSOLSpray (https://github.com/dafthack/MSOLSpray)
- MSOLSpray — Python — https://github.com/MartinIngesen/MSOLSpray
Below are the most common “ResultType”s you may see in the log when you use the tools mentioned above.
MFASweep
MFASweep PowerShell script checks MFA status of an account via a number of services within M365 (i.e. Graph API, Microsoft 365 Exchange Web Services etc). Black Hills Info Sec blog has a great write-up about exploitation of MFA inconsistencies.
Microsoft uses User-Agent strings to identify different types of devices, hence you will see the tools listed below using various User-Agents during their operations. Hence, MFASweep uses different User-Agent strings to attempt to simulate various devices.
Upon executing the following command with a valid pair of M365 credentials we can observe the log entries as shown in Figure 1.
Invoke-MFASweep -Username targetuser@contoso.com -Password ThisIsSuperSecure

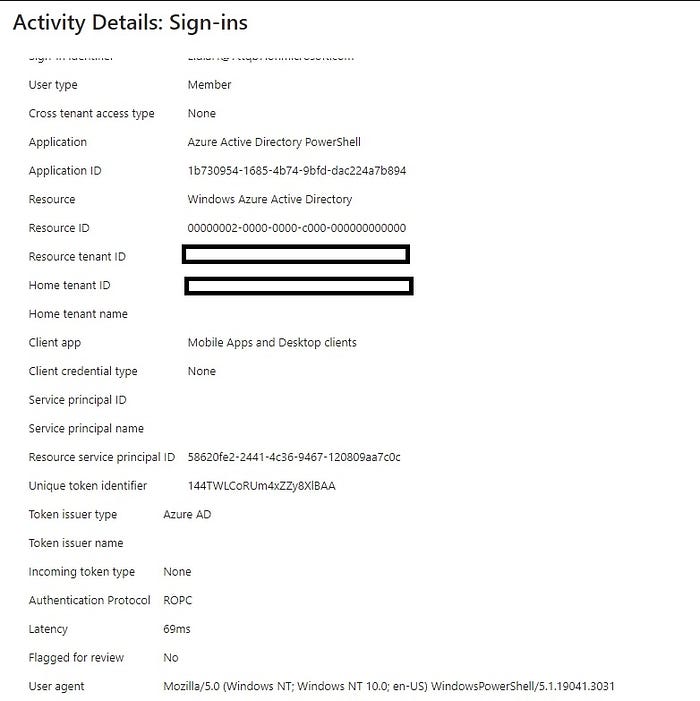
- A total of 3 events were noted. The event that had the status as “Interrupted” contained the value for Device Browser as “Android 4.0” and the Application always being “Office 365 Exchange Online”. The successful events contained interactions with the Microsoft Azure PowerShell and Azure Active Directory PowerShell.
- Both requests contained the User-Agent string as “ Mozilla/5.0 (Windows NT; Windows NT 10.0; en-US) WindowsPowerShell/5.1.19041.3031” (this will vary based on the PowerShell version used by the actor). Authentical protocol for both instances was ROPC.
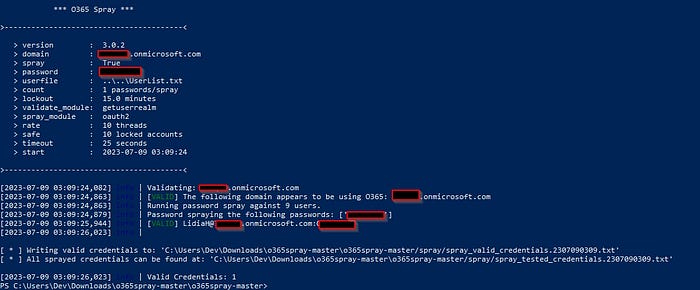
o365spray
o365spray is a python script that can be used to enumerate user accounts and for password spraying M365 users.
o365spray.py — spray -U list.txt — password ThisIsSuperSecure — domain contoso.com
The user Lidia Holloway as per Figure 3 log indicates a signin failure. The local output of o365spray indicates it as working credentials (see Figure 4). Though the credentials were valid, the App that was targeted was not installed in the M365 tenancy.
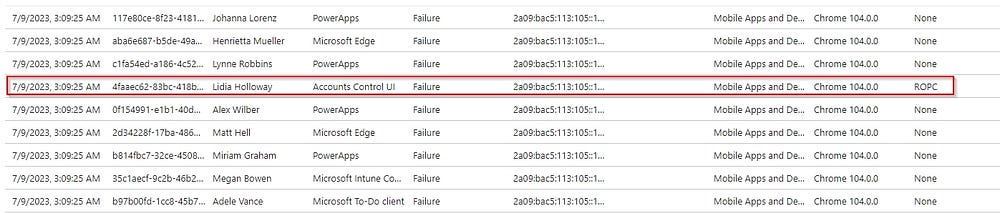
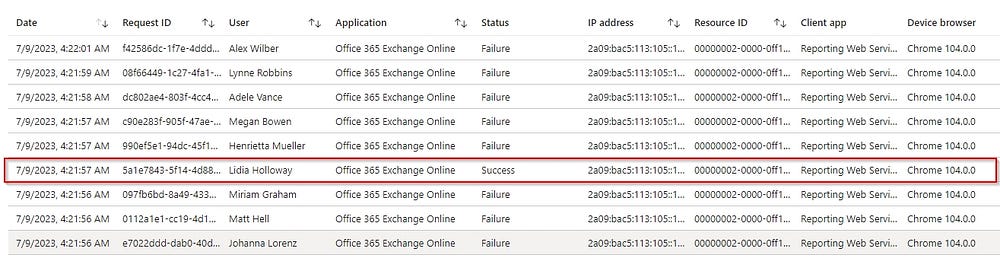
If specific spray modules are used then the client application remains the same across all the users who are targeted in the attack (see Figure 5 — reporting module). The User-Agent string was “
Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/104.0.0.0 Safari/537.36” across all the events for this run.
MSOLSpray — (Python)
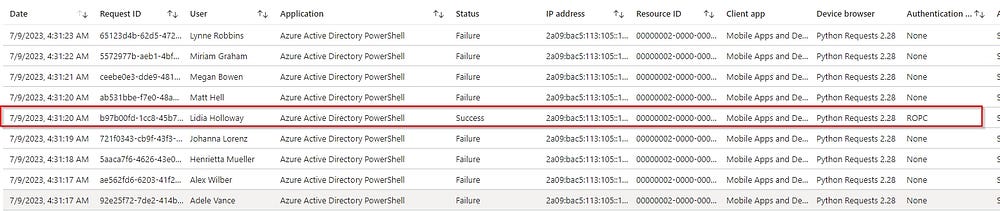
Following characteristics were observed in the M365 logs when MSOLSpray python version was executed:
- Application was always Azure Active Directory PowerShell
- User-Agent string started with python-requests
- Authentication protocol used in successful authentication was ROPC
MSOLSpray — (PowerShell)

- Application was always Azure Active Directory PowerShell
- User-Agent string contains WindowsPowerShell
- Authentication protocol used in successful authentication was ROPC
Potential Detection Opportunities
Following use detection use cases should be constrained to a short time window.
- Signin activity from the same source IP to multiple users where the User-Agent string contains PowerShell or python-requests.
- Signin activity where same application ID exists for authentication records for different users, but from the same source IP.
- Signin activity where different application IDs exists for authentication records for different users but from the same source IP.
#dfir #threatdetection #m365
